
Tesla CEO Elon Musk, who attended a meeting of the National Governor’s Association in Rhode Island, USA in July 2017, joked that in principle, if someone hacked into a self-driving Testra vehicle, he could be ordered to send all vehicles to Rhode Island. Threw it. However, according to reports, a vulnerability that could remotely control Tesla vehicles at once was discovered months before his remarks.
Jason Hughes, owner of Tesla vehicles, has been selling parts to hack and modify Tesla vehicles to unlock unannounced features and is a well-known figure in the Tesla community. He also worked as a white hacker to find and report vulnerabilities in car firmware and systems, including Tesla, to manufacturers.
When Tesla launched a service that transmits the location or situation of the charging supercharger to the navigation system, he conducted a system analysis and discovered a vulnerability that could enable vehicle access to the server side providing the service to obtain data from the world’s supercharger charger stations. did.
He reported the vulnerability to Tesla, and Tesla paid him $5,000 in compensation under the bug reporting program. Based on this incident, Hughes is said to have actively sought Tesla vulnerabilities.
Hughes discovered a vulnerability in the Tesla system in 2017. It is a function that receives data in real time from all Tesla vehicles and provides machine learning feedback to the AI installed in Tesla. Hughes succeeded in accessing the Tesla server Mothership, which they use for this learning communication, through a car VPN connection.
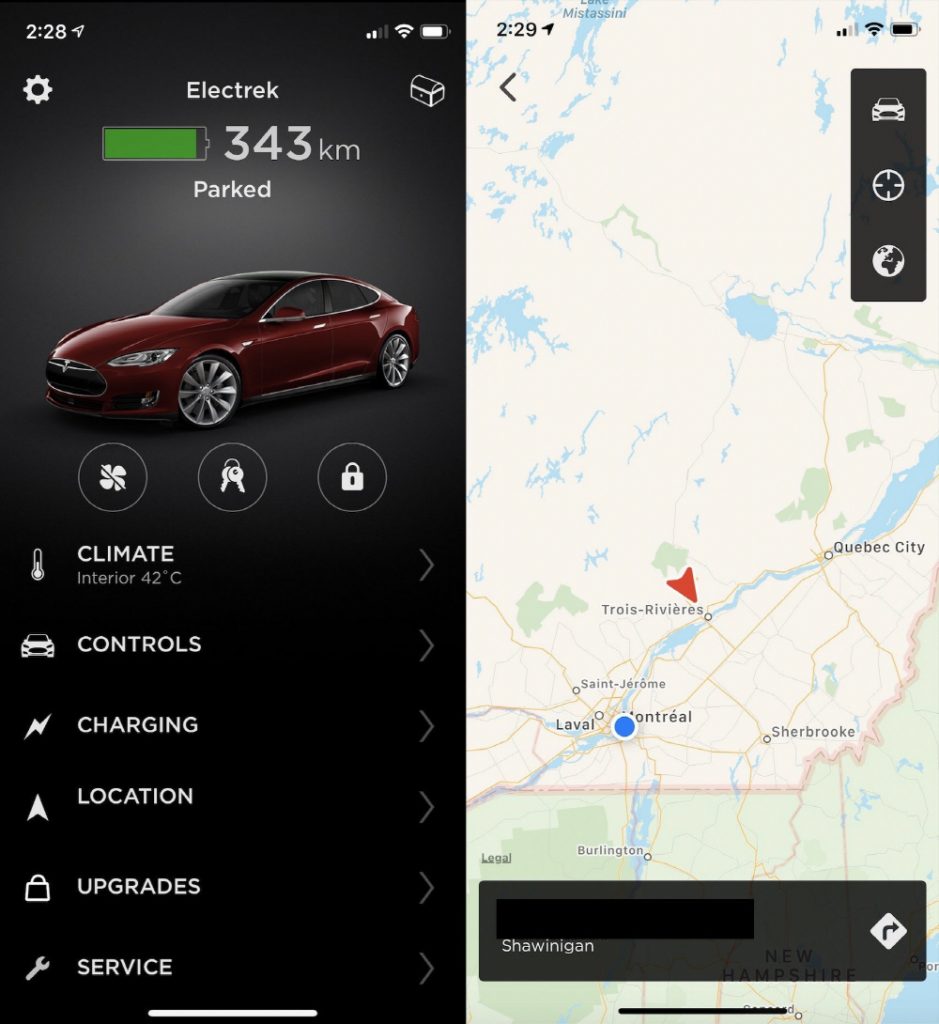
He realized that with a vehicle identification number, Mothership had full control over the vehicle. It was also possible to send commands to all vehicles by accessing it through the Tesla database. In fact, when he passed the identification number of a car at the time, he immediately pulled out data such as vehicle location information and battery level.
In addition, Hughes reported the vulnerability to the then-Tesla software security manager, and manipulated the California-based Tesla vehicle from a North Carolina home 3,800 km away. Tesla corrected the system based on the information provided by Hughes and immediately began protecting the network. Hughes received a special payment of $50,000, up to 10 times the bug compensation cap.
Tesla introduced Pwn2Own, a hacking program that paid a $1 million bounty for its vehicles in January 2020. Tesla said that since the launch of its first bug bounty program in 2014, Tesla has continued to increase its investment in partnerships with security researchers, and that the program will continue to improve the design of intrinsically safe systems. Related information can be found here .


















Add comment