
Apple’s lost and found tracker, AirTag, has a feature that allows you to know the owner’s contact information by scanning an AirTag dropped by someone with an NFC-enabled smartphone. However, a security researcher report revealed that this feature has the potential to be exploited for phishing.
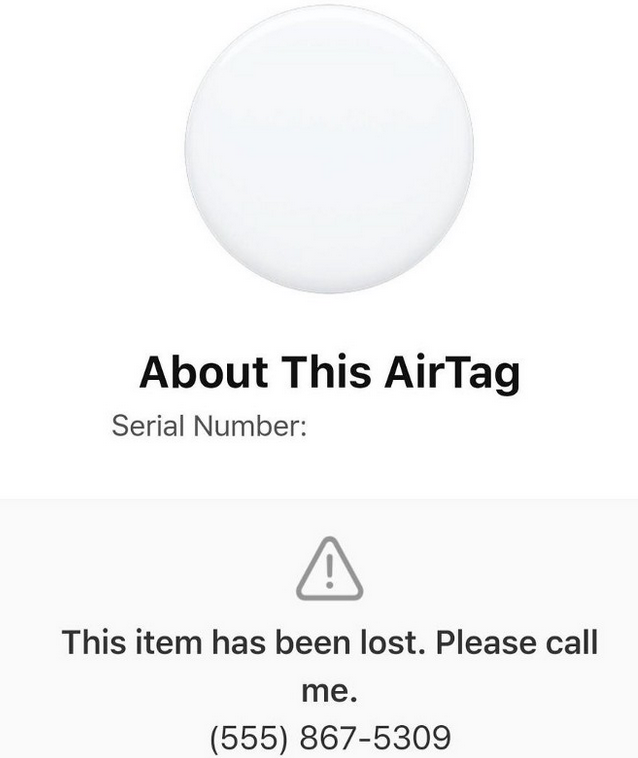
When AirTag is set to Lost Mode, a unique URL is created within the site (https://found.apple.com), where the AirTag owner can enter contact information, such as a phone number or email address. The person who scans this air tag is automatically guided to the URL to know the owner’s contact information. There is no need to log in or enter personal information to view your contacts.
According to security research team KrebsonSecurity, this lost mode cannot prevent users from putting arbitrary computer code into the phone number field, so anyone who scans the airtag will be redirected to a fake iCloud login page or other malicious site. can
Therefore, it is possible that someone who does not know that personal information is not required to view AirTag information is tricked into providing iCloud login information and other personal information, or downloading malware from redirects.
The possibility of the AirTag Lost Mode being exploited has been pointed out before. However, this required certain skills, such as the need to modify the airtag. On the other hand, this method can be more risky because it only inserts the code into the input field that Apple has officially prepared.
This vulnerability was originally discovered by a security consultant (Bobby Raunch). He also said he can’t remember any examples of such consumer miniature tracking devices becoming low-cost weapons. He contacted Apple on June 20 and said that after a three-month investigation, he was finally asked not to speak publicly about this vulnerability in a future update.
However, Apple did not answer questions about whether he was eligible for the bug bounty program or whether he would give him a prize, and it is said that the information was shared through Krebson Security.
Krebson Security is suggesting that the vulnerability could expose the good Samaritan attack, putting others at risk. As the AirTag lost and found tracking network itself relies on good intentions for Apple product users, they want Apple to respond quickly. Related information can be found here.


















Add comment