Security company Symantec has announced that the new malicious code, W32.Beapy, which unauthorizedly decrypts passwords, is increasing rapidly in companies.
Biffy is using hacking tools from the US National Security Agency (NSA) and spreading throughout the enterprise network, denying the majority of computers to crack passwords. Since its first discovery in January, more than 12,000 cases have been reported in 732 organizations since March. More than 80% of the infections occurred in China.
According to Symantec, Biffy spreads an Excel file that hides malicious code as an attachment to an email. When an email recipient opens the attachment, the NSA-developed backdoor tool, Double Pulse, is downloaded. Double Pulse uses ETERNAL Blue, which is the NSA vulnerability exploit tool, as well as Ransomware spread in 2017. It also adopted Mimikatz, a well known open source information gathering tool, which collects and spreads the passwords of infected computers to the corporate network.
According to reports, Kryptojacking has declined in recent months as Coin Hive, an online mining service, ends. However, file-type Cryptojacking malware, such as Biffy, is much more efficient and can be mined quickly, so hackers can earn more cryptography.
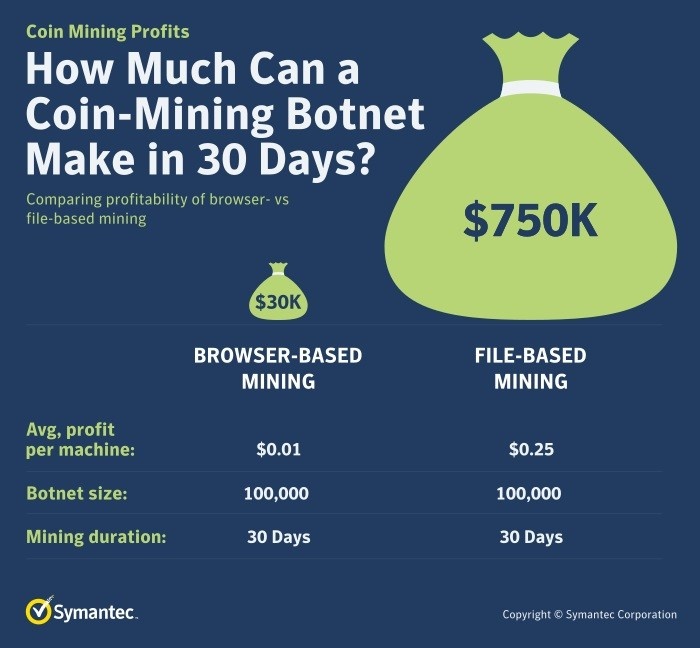
Symantec says file-based mining has reached a maximum of $ 750,000 if online-based mining income lasts only $ 30,000 a month. For more information, please click here .


















Add comment