
On June 6 (local time) in Europe, there was traffic that had to end in Europe over two hours in China. It was the Swiss hosting company that made the mistake, but China Telecom, China’s biggest ISP, approved it and the situation got worse.
In fact, traffic that has never been involved has never been through China Telecom. In April 2010, 15% of the world’s Internet traffic traversed a Chinese server. This includes traffic from the US government, military and NASA, as well as corporate sites such as Dell and Microsoft.
In the past six days, Swiss companies have made BGP (Border Gateway Protocol) route leak misses, and they have brought in a significant amount of mobile traffic from ISPs in France, Switzerland and the Netherlands. The mobile network went down or the effect of the debit card payment or Internet connection was slow. Communication quality is degraded.
Of course, there is no way to know whether China Telecom was intentionally confused. However, according to a study conducted by the US Naval College and Tel Aviv University in October, 2018, China Telecom said it has redirected to China by intercepting traffic in the United States or across the United States for several days, weeks, and months. Leakage of the BGP route itself is a frequent mistake, but at the time of the study it was considered malicious intent.
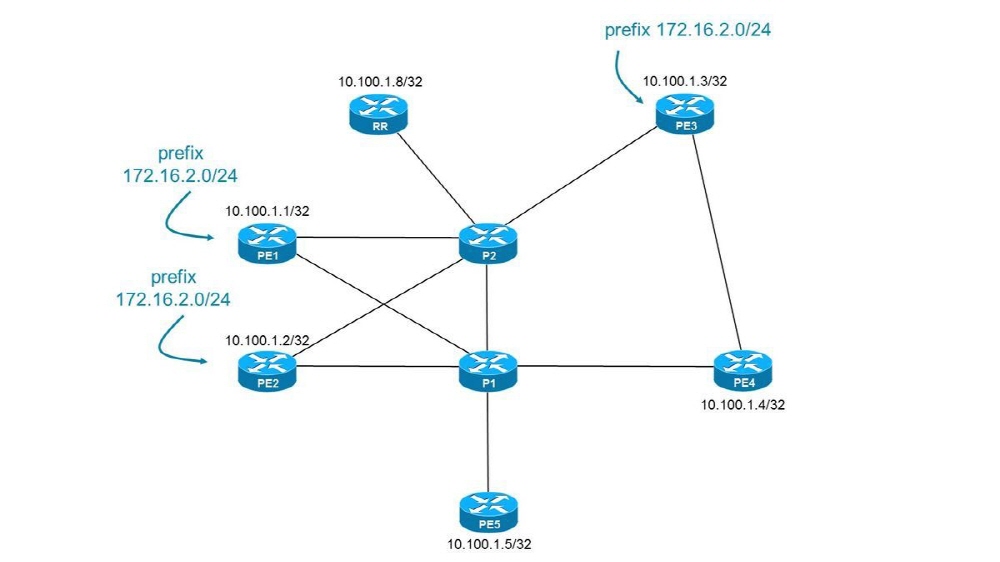
BGP serves to indicate the optimal route for Internet traffic from A to B destinations. It is a protocol that manages the Internet route. If you do not apply it properly, traffic will be scattered all over the place. The Internet has a network called an autonomous system (AS) owned by an ISP or a hosting company, which is like a map that tells each other what information is best for an address. Usually, all ASs have the right information, but occasionally someone may send the wrong information. For this reason, many ASs take measures to ignore false information.
China Telecom was an ISP that did not take such measures. First, the SafeHost data center in Switzerland leaked internal route information incorrectly to China Telecom. In a typical AS this data is ignored and nothing happens. However, Chan No Telecom has copied the wrong data to his information and sent it to the whole Internet. That’s why China Telecom sent information that it was a shortcut to reach a safe host or nearby network, and the traffic in Europe led to China Telecom.
This problem indicates that BGP routing is a problem for worldwide Internet communications. This is not happening if China Telecom has only a basic routing safety net and has timely detected and responded to route outflows. For more information, please click here .


















Add comment