It turned out that there was an attempt to plant a backdoor in a password wallet and steal a user’s bit coin using an open source code library. This case is simply telling the crisis of supply chain attack on open source software.
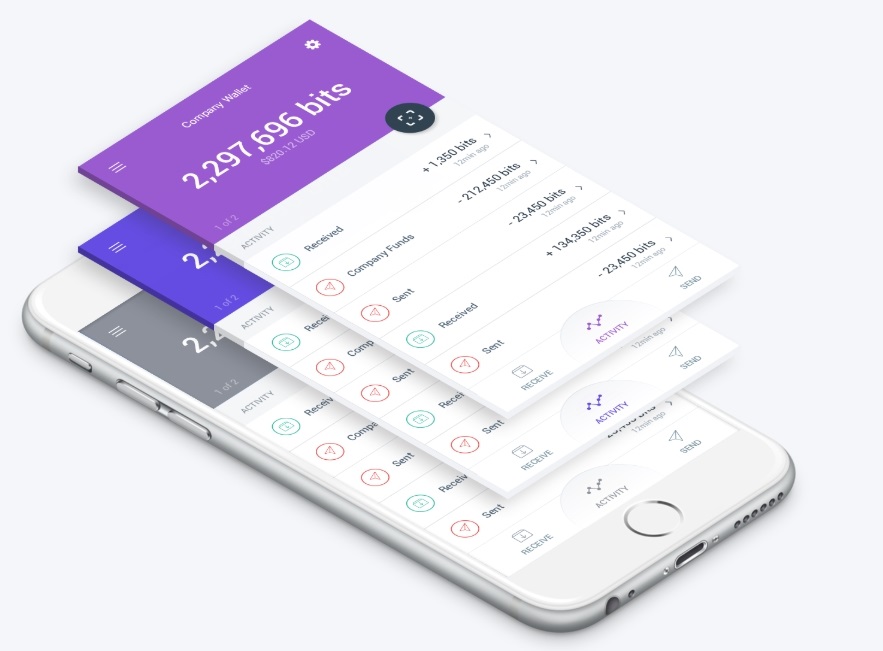
A bit coin purse app with a back door that steals bit coins is Copay. You can verify that you have a backdoor on the code-library (event-stream) used in the COPE app by checking the code reported on the official Hub’s bulletin board.
Verification results show that there is a problem with the specific module (flatmap-stream) introduced in version 3.3.6 of this code library released on September 8th. At the time of version release, the module itself was not vulnerable. By the way, October 10th, I have planted a backdoor in this module with a 2-step process including malicious code. This backdoor is designed for the purpose of stealing the bit coin held by the users of the COPY app.
It was pointed out that malicious code was entered into COPEY as a result of the issue on the bulletin board, but until October 11, COPEY did not take any other action. Initially, it claimed that it did not introduce modules with malicious code in the COPY app, but admitted that it was affected by backdoor from version 0.0.2 to 5.1.0 of the COPE app on November 26th. Users of these versions also recommended that you do not run the app until you update to the latest version, 5.2.0.
Package management tools According to NPM officials, this vulnerability is targeted not at general module developers but at some COPY developers with a specific development environment. The vulnerability also does not work on the developer’s computer, and developers have packaged features into end-user apps when they release their apps. For this reason, it was difficult to detect the attack in advance.
On the feather hub bulletin board, it was pointed out that the developer of this module did not have time to provide the updates and that they had been helped by other developers for several months. Open source software is an unspecified number of developers who have developed relationships. Sometimes malicious users can not detect malicious code silently. It is becoming more and more difficult to respond to cyber attacks targeting the open source supply chain, as developers are not making all the code, but are quickly developing new software using existing third-party components. For more information, please click here .


















Add comment